Table of Contents
Updated
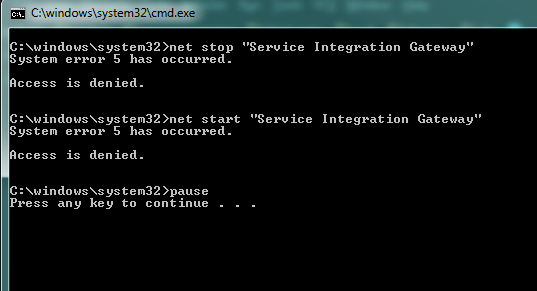
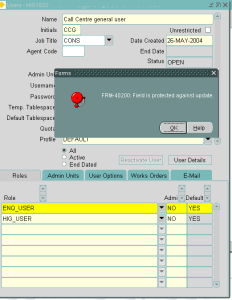
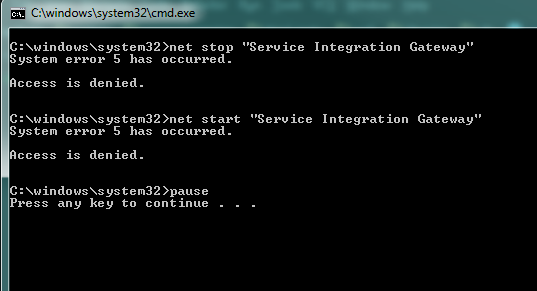
You should read these repair guidelines if your computer is denied access to Runas errors. g.In this scenario, when building to use the Run As command, 1 “Error 5: Access Denied” occurs. On its support site, Microsoft states, “This message is caused by the Discretionary Access Control (DACL) Subscriber List for the Secondary Connectivity Service not being considered configured correctly when performing an upgrade. Upgrades from Windows Server 2003 or Windows Server 2008.
g.
- 2 minutes to read.
This article provides workarounds for an issue where you cannot use the runas command, specifically the Run as administrator option or the Run as option. Another user after upgrading Windows Server.
Applies to: Windows Server 2012 R2
Original Knowledge Base Number: 977513
Symptoms
- They improve the Windows Server computer.
- You are logged in as a regular user.
- You are trying to use one of the following functions:
-
runascommand - Run Admin Option
- Run as another operator.
-
Access Denied
Reason
Discretionary Access Control (DACL) policies for the Secondary Logon Service are incorrectly configured during a Windows Server upgrade. This issue prevents the default from starting this service and starting a different application as a different user.
Workaround 1. Use The Sc.exe Command Line Utility
After completing the server upgrade, you can set the Sc.exe command line utility to its initial default configuration.
-
Open a command prompt window.
-
At a command prompt, type the following command and press ENTER:
clean stop of the selogone itself -
At the command prompt, enter the following purchase, and then press ENTER:
sc sdset seclogon D: (A ;; CCLCSWRPWPDTLOCRRC ;;; SY) (A ;; CCDCLCSWRPWPDTLOCRSDRCWDWO ;;; BA) (A ;; CCLCSWRPDTLOCRWD ;;; IU); A ;;; ARCR ;;; IU) (A ;; CCLCSWRPDTLOCRRC ;;; AU) S: (AU; FA; CCDCLCSWRPWPDTLOCRSDRCWDWO ;;; WD)Note
This command is included for readability.
-
Close the Command Prompt window.
-
Try using o From the following functions:
-
runascommand - Optional
- Run administrator only as another user.
Also make sure that you can switch users and that all secondary login services start correctly.
-
Workaround 2: Use Group Policy
The Group Policy Management Console can be used to configure a domain-based package that will set security by default after a server upgrade. New that a Group Policy Object (GPO) must be shared for this workaround. And it needs to be more tightly coupled so that the new GPOs only apply to the affected computers.
-
Change your Group Policy in the Group Policy Management Console.
-
Find the policy: Computer Configuration Policies Windows Settings Security Settings System Services.
-
Open the secondary login service.
-
Select the Set this policy setting for advice check box, and then select Enabled.

SetChange the service start mode manually.
-
Expand the security node to allow the following properties and objects.
property Objects Authenticated Users Request Model, Request Status, Dependency Enumeration, Start, Stop, Continue and Request, Read Permissions, Custom Controls Integrated Administrators Full Control Interactive Request model, request status, enumeration of dependencies, start, stop, continue, i.e. request, read permissions, user-defined control Service Request Template, Request Status, Dependency Enumeration, Pause, Continue and Request, Custom Control System Request Model, Request Status, List Dependents, Start, Suspend, Continue and Request, Stop -
Click OK to apply the security changes.
-
Click OK to apply the changes r uppa policy.
-
Apply the GPO to the affected computers while waiting for the policy to update or manually running the update.
-
Try one of the following:
-
runascommand - Run as administrator and see this parameter.
- Run another user option.
Also make sure you can switch users normally and that our own secondary login service starts correctly.
-
Additional Information
For more information on the runas command, visit my following Microsoft TechNet website:
For more information on using the Group Policy Management Console, visit the following Microsoft TechNet website:
You must be logged in as an administrator before running these commands.
We should never recommend this workaround as permissions are actually reapplied during Group Policy updates. However, the owners are notIt fixes false protection more than once after an update.
Feel like a jerk, but be careful, get more information.
The runas command depends on the secondary login service.On the system, my device is set to manual mode by default and is therefore not activated.
This is a valid legacy feature as far as I know and is probably why it doesn’t work.
EDIT:This is traditional because this command is older than UAC; MS will appreciate that you are using UAC instead of runas , which is more secure; You can invoke UAC by calling scripts through PowerShell with the -Verb RunAs
argument
answered Nov 18, 2018 at 9:22 am
189
answered Aug 7, 2017 at 10:43 pm
Make sure pedro burgos has easy access to this directory. For example, the user cannot easily access the directories of other telecom operators. You can test this generated theory by dragging and dropping the script to C: temp
. traffic
answered Apr 8 ’20 at 10:25
Updated
Are you tired of your computer running slow? Annoyed by frustrating error messages? ASR Pro is the solution for you! Our recommended tool will quickly diagnose and repair Windows issues while dramatically increasing system performance. So don't wait any longer, download ASR Pro today!

Speed up your computer today with this simple download.
Suggestions De Corrections De Bugs D’accès Refusé à Runas
Предложения по исправлению ошибок запрещены в доступе Runas
Runas åtkomst Nekad Buggfixningsförslag
Suggerimenti Per La Correzione Di Bug Negato Per L’accesso A Runas
Runas 액세스 거부 버그 수정 제안
Runas Access Denied Bug Fixes Suggestions
Runas-toegang Geweigerd Suggesties Voor Bugfixes
Runas Access Verweigert Vorschläge Zur Fehlerbehebung
Sugestie Dotyczące Odmowy Dostępu Do Runas
Acesso Negado Ao Runas E Sugestões De Correções De Bugs