Table of Contents
Updated
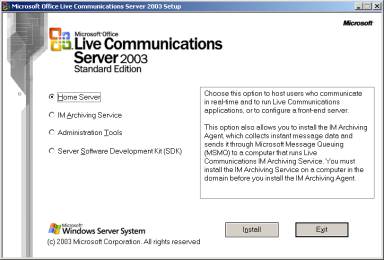
It appears that some of our users are experiencing a known bug in the Live Communications Server 2005 Service Pack. This issue occurs for a number of reasons. We will talk about this below. Live Communications Server 2005 (LCS 2005), codenamed Vienna, is arguably the second release of SIP-based instant messaging and presence server after Live Communications Server 2003. LCS 2005 was tentatively released in 2005 and updated to Upgraded with Service Pack 1 to reflect new features in 2006.
If steps 0 and 2 do not match those corresponding commands, please visit:
You can ask to increase the verbosity (255 is the highest), and if you have an SA, you can use a filter to focus on the one that interests you:
How do you troubleshoot IPSec?
Check security policies and routing.Look for upstream devices that do port and address translation.Apply debug window filters, recordings, or logs as needed to isolate the issue where targeted visitors are removed.
After you’ve configured Phases 1 and 2, but already have persistent two-way traffic problems, there are two things to keep in mind:
1. When you view this output of crypto ipsec sa, the picking will be expanded based on encapsulations. If it doesn’t, the far end may not receive return traffic. Confirm package tracking and / or tracking.
2. Use a packet tracker request (CLI or GUI) on the ASA to see how it is being processed The last stream is running. NAT and ACL problems can often be quickly identified using this tool.
Yesterday I really helped troubleshoot ASA VPN issues. The state ASA had to set up an IPSec VPN tunnel (also known as L2L between sites) for a large third party vendor without an ASA. The tunnel has not arrived yet.
It seems that the installation was there, not to mention a third party that said their installation was there too.
Check SA To See If They Are Forming
This is always considered my first troubleshooting step. The ASA VPN must have a Phase 1 SA and a Phase 2 SA.
In my case, there was no phase 1 SA, so there was no point in looking for phase 2 SA.
The ASA may not have noticed interesting traffic yet and has not tried to start its tunnel. You can try to plot this package:
Only a small amount of HTTP traffic is simulated from 10.0.0.1 to 172.16.0.1. This should allow hosts to communicate through the tunnel.
This does not work and no SA has been installed. So Phase 1 seems like a good place to focus.
Probelieve The Suggestions
The first step in troubleshooting phase 1 (in my case, IKEv2) is to confirm who has matching suggestions for the two moves. The proposals include acceptable combinations of all ciphers, hashes, and other cryptographic information.
Updated
Are you tired of your computer running slow? Annoyed by frustrating error messages? ASR Pro is the solution for you! Our recommended tool will quickly diagnose and repair Windows issues while dramatically increasing system performance. So don't wait any longer, download ASR Pro today!

This is not difficult if you control both ends of the ASA VPN tunnel. See what’s configured. In my case, this is more difficult to manage because the third party manages the support for the remote PC at the end of the tunnel.
This will confirm any errors with IKEv2 (you can restore IKEv1 if needed).
“64” is literally a debug level. It can range from 1 to 256. The higher the number, the more detail you get. Don’t get in too fast because there is too much information to dig. (16):
ikev2-proto-1: received directives:Sentence 1: AES-CBC-256 SHA1 SHA96 DH_GROUP_1024_MODP / Group 2Sentence 2: AES-CBC-256 SHA256 SHA256 DH_GROUP_1024_MODP / Group 2Sentence 3: AES-CBC-128 SHA1 SHA96 DH_GROUP_1024_MODP / Group 2Sentence 4: AES-CBC-128 SHA256 SHA256 DH_GROUP_1024_MODP / Group 2Sentence 2: 3DES SHA1 SHA96 DH_GROUP_1024_MODP / Group 2Proposition 6: 3DES SHA256 SHA256 DH_GROUP_1024_MODP / Group 2IKEv2-PROTO-1: (16): Error finding a matching policyIKEv2-PROTO-1: (16): Expected directives:Sentence 1: AES-CBC-256 SHA384 SHA384 DH_GROUP_2048_MODP_256_PRIME / Group 24
Here we can see that the remote endpoint has six offers, and we have one.
Our proposal does not match any of these, so IKE will fail. There are actually two ways to solve this problem:
- We will replace this sentence that matches yours.
- You change your offer so that our offer matches ours.
For testing purposes, it is generally easier to edit our site. Later, we can develop better security algorithms.
Once the proposal has been changed, these debug errors will not show up at all. But we still don’t get SA Phase 1.
How do I check my IPSec VPN status?
Choose. Network. IPSec tunnel. …Tunnel status. … Green indicates an active IPSec SA tunnel. Red indicates that the IPSec SA is unavailable or has expired.The state of the IKE gateway. … Green indicates a valid IKE Phase 1 SA.Tunnel interface state. … Green means that the tunnel interface is considered active.
Also, it looks like the ASA isn’t even trying to stop the tunnel. Suggestion errors originated from a remote station.
Check Path
There is another ASA on the way, incredibly, it seems like a good idea to check if it gets in the way.
We need to improve ESP and move to AH (however AH is definitely used in all environments). They do not work over IP, they are completely isolated protocols.
If I run the Edge Packet Tracer, I find that the wrong interface is being used for outgoing traffic. I won’t go into details, but there was a big problem with routing.
Additional Debugging
How do I debug VPN?
The ‘vpn debug ill no’ command enables debug mode for VPND, most VPN daemons. Debug data is written to the file $ FWDIR / log / vpnd. elg file. To turn it off, just type: wi vpn debug off ‘.
When I was working in Messer-ASA, packet capture revealed several substancesth:
- A third party regularly tried to connect us.
- Local ASA VPN did not work for ASA connections near space
This time we turn our attention to the platform. As soon as I run another packet tracer, I get an output that reveals an interesting problem:
IKEv2-PLAT-5: HANDLE PSH INVALIDIKEv2-PLAT-1: Error requesting another VPN license. The maximum number of tunnels has been reached and / or the license limit for starting a tunnel has been exceeded.IKEv2-PLAT-1: Asa Connect L2L Boot Failure
We almost always don’t need to worry too much about site-to-site tunnel certification on the ASA, but what’s going on here?
A quick Google search showed that this in turn can happen when ASA contexts are launched. Yes.
Luckily, this is probably a simple solution. All we need to do is create (or modify) a resource class via the system context and add it to that context.
How do I check my VPN traffic on ASA?
First I run the command: “show crypto isakmp sa”. This gives me a list of all VPN tunnels except their peer IP addresses. Most important inThe expressions we are now paying attention to are “packets are encapsulated” and “packets are decapitated”. Packaged boxes are the packages you push into the VPN.
vpn class Limit VPN resource Other 5%Context is our context VPN Member
This will affect 5% of our licenses in the context of ASA VPN. Back in context, I can see that SA is finally formingand now VPN is on.
Conclusion
It went wrong with this particular ASA VPN and connection that either one of them could disrupt the channel. This made it so interesting and therefore should be documented here.
We have covered several troubleshooting methods. Obviously this is not an efficient list, but I hope the technique will help you in the future.
- Understand how IPSec works.
- Use two show SA commands
- Use the debug commands from Step 2
Melhor Maneira De Desinstalar O Live Communications Server 2005 Service Pack
Il Modo Migliore Per Disinstallare Il Service Pack Di Live Communications Server 2005
Beste Manier Om Live Communications Server 2005 Service Pack Te Verwijderen
Live Communications Server 2005 서비스 팩을 제거하는 가장 좋은 방법
La Mejor Manera De Desinstalar Live Communications Server 2005 Service Pack
Bästa Sättet Att Avinstallera Live Communications Server 2005 Service Pack
Meilleur Moyen De Désinstaller Live Communications Server 2005 Service Pack
Najlepszy Sposób Na Odinstalowanie Live Communications Server 2005 Service Pack
Лучший способ удалить пакет обновления Live Communications Server 2005
Beste Methode Zum Deinstallieren Von Live Communications Server 2005 Service Pack