Updated
1. Download ASR Pro
2. Run the program
3. Click "Scan Now" to find and remove any viruses on your computer
Speed up your computer today with this simple download.
Over the past few days, some of our users have encountered a well-known eac log checksum verification error message. This problem occurs for several reasons. Let’s get to know them below.
<primary role="primary"><element></p>
<div>
<p>When Exact Audio copies a log file after ripping a large CD, a tool exists that evaluates whether the log file has been corrected. There is a special file “CheckLog.exe” in the EAC folder</p>
<p>Create a .bat file, just open notepad, paste the code below and save it with any name. Then remove the “.txt” file extension and replace it with “.bat”.</p>
<pre><code>@echo off"C:Program Files (x86)Exact Audio CopyCheckLog.exe" %1stop</code></pre>
<p>Save the .bat file anywhere on your computer. You can drag and drop the .log file right after checking.</p>
<p>If you want to take it one step further, you can use the code check below on different .log files at the same time. Just create an attached .bat file and paste the laws below. This allows you to upload a bunch of .log files for you to explore. OffIf </p>
<p><img src="/posts/check-eac-log-checksum.png" style="margin-top:20px; margin-bottom:20px; display: block; margin: 0 auto;" alt="check eac log checksum"></p>
<pre><code>@echo [%1]==[] visiting:eof:Ribbon%1 echo check:"C:Program Files Audio (x86)exact CopyChecklog.exe" %1Echo.Echo.changeotherwise [%1]==[] go to loopstop</code></pre>
<p>If the manually saved log file is correct, the following is displayedalt=””:</p>
<div><img loading="lazy" size="(max-width: 450px) 100vw, 450px" src="https://captainrookie.com/wp-content/uploads/2018/09/ok .png" srcset ="https://captainrookie.com/wp-content/uploads/2018/09/ok.png 450w, https://captainrookie.com/wp-content/uploads/2018/09/ok-300x80.png 300 Tue"></div>
<p>If the .log information seems to have changed, what is actually shown is what follows alt=””:</p>
<div><img size="(max-width: loading="lazy" 100vw, 450px) 450px" src="https://captainrookie.com/wp-content/uploads/2018/09/edit.png" srcset ="https://captainrookie.com/wp-content/uploads/2018/09/edit.png 450w, https://captainrookie.com/wp-content/uploads/2018/09/edit-300x80.png will be 300 Tue "></div>
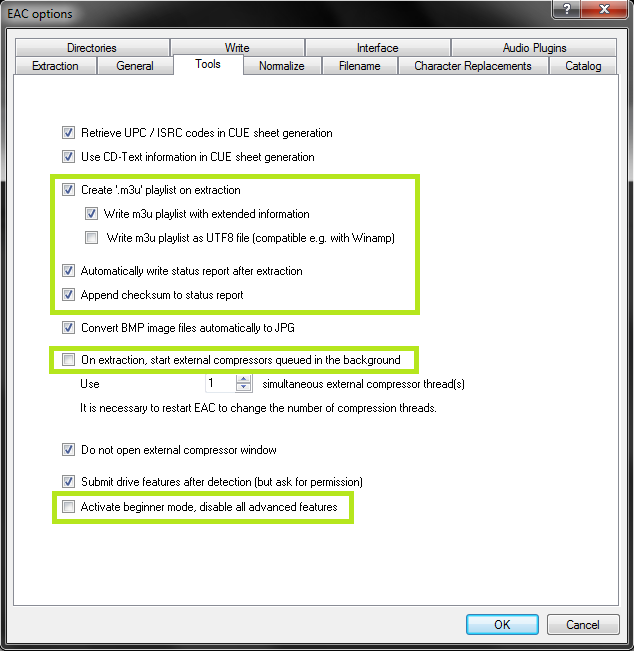
<p>This will probably only work if a checksum is added to the log file when it is written. EAC v1.0 Beta 1 and later.</p>
<p>Enable in configurations: Eac Parameters –> EAC –> Shortcut tools, then check the “add to name report” checksum</p>
<div><img alt="" loading="lazy" size="(max-width: 622px) 100vw, 622px" src="https://captainrookie.com/wp-content/uploads/2018/09/EAC_2018 -09-28_22-16-24.png" srcset="https://captainrookie.com/wp-content/uploads/2018/09/EAC_2018-09-28_22-16-24.png 622w, https://captainrookie .com/wp-content/uploads/2018/09/EAC_2018-09-28_22-16-24-291x300.291w"></div>
</div>
<p></item></main></section>
<p>When png Exact Copy Audio creates a log file after copying a CD, there is a tool that evaluates if the file was logged The label has only been changed. There is a CheckLog.exe file in the EAC folder</p>
<p>Create a .bat report by opening Notepad, paste the code below and save it as you wish. Then remove the “.txt” file extension, replacing it with “.bat”.</p>
<pre><code>@echo off"C:Program Files (x86)Exact Audio CopyCheckLog.exe" %1stop</code></pre>
<p>Save the .bat file anywhere on your computer. Can you then easily drag and drop the .log file onto it to examine it. .You .</p>
<div style="background: rgba(156, 156, 156, 0.07);margin:20px 0 20px 0;padding:20px 10px 20px 10px;border: solid 1px rgba(0,0,0,0.03);text-align: left;"><h2><span class="ez-toc-section" id="Updated-2"></span>Updated<span class="ez-toc-section-end"></span></h2>
<p>Are you tired of your computer running slow? Annoyed by frustrating error messages? <a href="https://link.advancedsystemrepairpro.com/d7b96561?clickId=geeksofknowhere.com" target="_blank" rel="nofollow">ASR Pro</a> is the solution for you! Our recommended tool will quickly diagnose and repair Windows issues while dramatically increasing system performance. So don't wait any longer, download <a href="https://link.advancedsystemrepairpro.com/d7b96561?clickId=geeksofknowhere.com" target="_blank" rel="nofollow">ASR Pro</a> today!</p>
<br><a href="https://link.advancedsystemrepairpro.com/d7b96561?clickId=geeksofknowhere.com" target="_blank" rel="nofollow" alt="download"><img src="/wp-content/download5.png" style="width:340px;"></a></div>
<p>If .you .want .to .learn .more, .you .can .check .several .log .files at once with the following code. Just create another .bat file and paste each of our codes below. .This .allows you to .drag and drop a bunch of .log clips onto it for viewing.</p>
<pre><code>@echo off[%1]==[]if we go from echo to %1:"C:Program :eof:Ribboncheck Files Audio (x86)exact CopyChecklog.exe" %1Echo.Echo.changeotherwise [%1]==[] go to loopstop</code></pre>
<p>If the .indicator file is correct, you will see:</p>
<p>If the .log file appears to have been modified, you will see in particular:</p>
<p>This will probably only work if the log file provides a checksum when written to by the application. EAC v1.0 Beta 1 and later.</p>
<p>Enable. In settings: EAC -> EAC Options -> “Tools”, tab check “Checksum” and “Add symbol report” </p>
<p><img loading="lazy" alt="" size="(max-width: 450px) 450px" 100vw, src="https://captainrookie.com/wp-content/uploads/2018/09/ok.png" srcset="https://captainrookie.com/wp-content/uploads/2018/09/ok.png 450w, https://captainrookie.com/wp-content/uploads/2018/09/ok-300x80.png 300W"><img alt="" loading="lazy" size="(max-width: 450px) 100vw, 450px" src="https://captainrookie.com/wp-content/uploads/2018/09/edit.png" srcset="https://captainrookie.com/wp-content/uploads/2018/09/edit.png 450W, https://captainrookie.com/wp-content/uploads/2018/09/edit-300x80.png 300W"><img alt="" loading="lazy" size="(max-width: 622px) 100vw, 622px" src="https://captainrookie.com/wp-content/uploads/2018/09/EAC_2018-09- 28_22-16-24.png" srcset="https://captainrookie.com/wp-content/uploads/2018/09/EAC_2018-09-28_22-16-24.png 622w, https://captainrookie.com/ wp-content/uploads/2018/09/EAC_2018-09-28_22-16-24-291x300.png 291w"> <block quote></p>
<p>Do you want this recorder to use protocols like EAC or be EAC compatible?</p>
</blockquote>
<p>This is known because, at the time, it seemed that using an EAC-type registrar was more likely to detect wippers supported by private trackers. In the meantime, the udls have changed and the Whipper has evolved. Today I think an internal logger (YAML-like beater) would be better: IStill not sure if it will be compatible with Whiipper v0.6.0. <g-emoji alias="smile" fallback-src="https://github.githubassets.com/images/icons/emoji/unicode/1f604.png implementation">😄</g-emoji></p ><block quote></p>
<p>I have an EAC protocol signing algorithm in python a few months ago. Code</p>
</blockquote>
<p><block quote></p>
<p>This is ugly, but very short and can easily be integrated to create protocols indistinguishable from EAC.</p>
</blockquote>
<p>I don’t know what was behind the introduction of the EAC file checksum: I think it was an attempt to thwart attempts by users to forge records (which is usually doomed in the country of private trackers). I think it is (you can’t interfere uselessly with the recording) and I’m not sure if it’s our own motives.<br />Sorry to answer your topic (with a partial answer and) one more thing of yours: opinion, what are the specific benefits of adding a verifiable EAC control log to <code>morituri-eaclogger</code>?</p>
<p><img src="https://doujinstyle.com/eac/ripping/3.png" style="margin-top:20px; margin-bottom:20px; display: block; margin: 0 auto;" alt="check eac log checksum"></p>
<p>This should be a cover letter, but at least it deserves a great announcement…</p>
<p>The EAC validation method is outdated and compromised. Attackers can add trusted control entitiesWe are in compromised log files. Unfortunately, this technology is widely used by others and trackers, we sincerely hope that our members have enough strength not to try to change the application protocol, as this will lead to a permanent ban. We hope that thanks to the Freeleeches materials, our and users managed to achieve a sufficient number of buffers, without reaching the maximum and without resorting to the described system. . We don’t think my users will waste their time trying protocols to change to get buffers.fail</p>
<p>Typical when using this method: a good solid 0.99 is simulated to look like a huge 1.0 with a success checksum generated by checking the log verifier for 100% respectively. This doesn’t mean it’s a transcode, it basically means we can no longer check much of Log-eac’s authenticity (XLD might be ok for now, but we trust NWCD with our newer version of the family tree tool, especially metadata function.</p>
<p>EAC still allows downloadstime, because we hope that our user base will register fake logs.</p>
<p>All unverified torrents are NOT active and can be trumped, we can notify the community when a particular trump starts. We’re making our next plan for the FIRST FLAC milestone – Motorola more on that in a moment. The system check went through all the old separate logs immediately and checks every new boot.</p>
</p>
<a href="https://link.advancedsystemrepairpro.com/d7b96561?clickId=geeksofknowhere.com" target="_blank" rel="nofollow"> Speed up your computer today with this simple download. </a>
</p>
<p><a href="https://geeksofknowhere.com/pt/um-caminho-facil-para-verificar-a-soma-de-verificacao-de-cada-log/" class="translate">Verifique A Soma De Verificação De Cada Log</a><br /> <a href="https://geeksofknowhere.com/nl/een-gemakkelijke-manier-om-ervoor-te-zorgen-dat-u-de-controlesom-van-elk-logboek-controleert/" class="translate">Controleer Elk Logboekcontrolesom</a><br /> <a href="https://geeksofknowhere.com/ru/%d0%bf%d1%80%d0%be%d1%81%d1%82%d0%be%d0%b9-%d1%81%d0%bf%d0%be%d1%81%d0%be%d0%b1-%d1%81%d1%80%d0%b0%d0%b2%d0%bd%d0%b8%d1%82%d1%8c-%d0%ba%d0%be%d0%bd%d1%82%d1%80%d0%be%d0%bb%d1%8c%d0%bd%d1%83%d1%8e/" class="translate">Проверить контрольную сумму журнала Eac</a><br /> <a href="https://geeksofknowhere.com/es/una-manera-muy-facil-de-comprobar-la-suma-de-comprobacion-de-casi-el-registro/" class="translate">Compruebe La Suma De Comprobación De Registro De Eac</a><br /> <a href="https://geeksofknowhere.com/sv/ett-enkelt-och-enkelt-satt-att-kontrollera-kontrollsumman-for-varje-enskild-logg/" class="translate">Kontrollera Eac Log Checksum</a><br /> <a href="https://geeksofknowhere.com/it/un-modo-abbastanza-semplice-per-controllare-il-checksum-di-ogni-singolo-log/" class="translate">Controllare Il Checksum Del Registro Di Eac</a><br /> <a href="https://geeksofknowhere.com/pl/latwy-sposob-na-sprawdzenie-sumy-kontrolnej-kazdego-dziennika/" class="translate">Sprawdź Sumę Kontrolną Dziennika Eac</a><br /> <a href="https://geeksofknowhere.com/ko/%eb%aa%a8%eb%93%a0-%eb%8b%a8%ec%9d%bc-%eb%b0%8f-%eb%aa%a8%eb%93%a0-%eb%a1%9c%ea%b7%b8%ec%9d%98-%ec%b2%b4%ed%81%ac%ec%84%ac%ec%9d%84-%ed%99%95%ec%9d%b8%ed%95%98%eb%8a%94-%eb%ac%b8%ec%a0%9c-%ec%97%86/" class="translate">EAC 로그 체크섬 확인</a><br /> <a href="https://geeksofknowhere.com/fr/un-moyen-simple-de-payer-la-somme-de-controle-de-chaque-journal/" class="translate">Vérifier La Somme De Contrôle Du Journal Eac</a><br /> <a href="https://geeksofknowhere.com/de/eine-einfache-vorgehensweise-um-die-prufsumme-jedes-protokolls-zu-uberprufen/" class="translate">Überprüfen Sie Die Prüfsumme Der Einzelnen Protokolle</a></p>
<div class="saboxplugin-wrap" itemtype="http://schema.org/Person" itemscope itemprop="author"><div class="saboxplugin-tab"><div class="saboxplugin-gravatar"><img src="https://geeksofknowhere.com/wp-content/uploads/lukecole.jpg" width="100" height="100" alt="Luke Cole" itemprop="image"></div><div class="saboxplugin-authorname"><a href="https://geeksofknowhere.com/author/lukecole/" class="vcard author" rel="author" itemprop="url"><span class="fn" itemprop="name">Luke Cole</span></a></div><div class="saboxplugin-desc"><div itemprop="description"></div></div><div class="clearfix"></div></div></div><div class='yarpp yarpp-related yarpp-related-website yarpp-template-thumbnails'>
<!-- YARPP Thumbnails -->
<h3>Related posts:</h3>
<div class="yarpp-thumbnails-horizontal">
<a class='yarpp-thumbnail' rel='norewrite' href='https://geeksofknowhere.com/en/how-to-check-windows-error-log/' title='Troubleshooting Tips On How To Check The Windows Error Log'>
<img width="150" height="150" src="https://geeksofknowhere.com/wp-content/uploads/2021/09/how-to-check-windows-error-log-150x150.png" class="attachment-thumbnail size-thumbnail wp-post-image" alt="" loading="lazy" data-pin-nopin="true" srcset="https://geeksofknowhere.com/wp-content/uploads/2021/09/how-to-check-windows-error-log-150x150.png 150w, https://geeksofknowhere.com/wp-content/uploads/2021/09/how-to-check-windows-error-log-120x120.png 120w" sizes="(max-width: 150px) 100vw, 150px" /><span class="yarpp-thumbnail-title">Troubleshooting Tips On How To Check The Windows Error Log</span></a>
<a class='yarpp-thumbnail' rel='norewrite' href='https://geeksofknowhere.com/en/error-code-pxe-e61-media-test-failure-check-cable/' title='Troubleshoot Pxe-e61 Error Code Bracket Test Failed Check Cables Easily'>
<img width="150" height="150" src="https://geeksofknowhere.com/wp-content/uploads/2021/12/error-code-pxe-e61-media-test-failure-check-cable-150x150.jpg" class="attachment-thumbnail size-thumbnail wp-post-image" alt="" loading="lazy" data-pin-nopin="true" srcset="https://geeksofknowhere.com/wp-content/uploads/2021/12/error-code-pxe-e61-media-test-failure-check-cable-150x150.jpg 150w, https://geeksofknowhere.com/wp-content/uploads/2021/12/error-code-pxe-e61-media-test-failure-check-cable-120x120.jpg 120w" sizes="(max-width: 150px) 100vw, 150px" /><span class="yarpp-thumbnail-title">Troubleshoot Pxe-e61 Error Code Bracket Test Failed Check Cables Easily</span></a>
<a class='yarpp-thumbnail' rel='norewrite' href='https://geeksofknowhere.com/en/an-error-occurred-while-validating-the-server-dns/' title='Best Way To Troubleshoot DNS Server Check Error'>
<img width="150" height="150" src="https://geeksofknowhere.com/wp-content/uploads/2021/12/an-error-occurred-while-validating-the-server-dns-150x150.jpg" class="attachment-thumbnail size-thumbnail wp-post-image" alt="" loading="lazy" data-pin-nopin="true" srcset="https://geeksofknowhere.com/wp-content/uploads/2021/12/an-error-occurred-while-validating-the-server-dns-150x150.jpg 150w, https://geeksofknowhere.com/wp-content/uploads/2021/12/an-error-occurred-while-validating-the-server-dns-120x120.jpg 120w" sizes="(max-width: 150px) 100vw, 150px" /><span class="yarpp-thumbnail-title">Best Way To Troubleshoot DNS Server Check Error</span></a>
<a class='yarpp-thumbnail' rel='norewrite' href='https://geeksofknowhere.com/en/read-verification-failed-error-0000/' title='Best Way To Get Rid Of Read Check Error 0000'>
<img width="150" height="116" src="https://geeksofknowhere.com/wp-content/uploads/2021/12/read-verification-failed-error-0000-150x116.jpg" class="attachment-thumbnail size-thumbnail wp-post-image" alt="" loading="lazy" data-pin-nopin="true" /><span class="yarpp-thumbnail-title">Best Way To Get Rid Of Read Check Error 0000</span></a>
</div>
</div>
</div><!-- .entry -->
<div class="post-tags clr">
<span class="owp-tag-text">Tags: </span><a href="https://geeksofknowhere.com/tag/cafa/" rel="tag">cafa</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/checksum-error/" rel="tag">checksum error</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/crc/" rel="tag">crc</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/cue-sheet/" rel="tag">cue sheet</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/exact-audio-copy/" rel="tag">exact audio copy</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/extraction/" rel="tag">extraction</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/filename/" rel="tag">filename</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/hamming-code/" rel="tag">hamming code</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/hash/" rel="tag">hash</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/integrity/" rel="tag">integrity</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/log-file/" rel="tag">log file</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/md5/" rel="tag">md5</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/owens-presentation/" rel="tag">owens presentation</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/quaternary-checksum/" rel="tag">quaternary checksum</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/rip/" rel="tag">rip</a><span class="owp-sep">,</span> <a href="https://geeksofknowhere.com/tag/sha1/" rel="tag">sha1</a></div>
<nav class="navigation post-navigation" aria-label="Read more articles">
<h2 class="screen-reader-text">Read more articles</h2>
<div class="nav-links"><div class="nav-previous"><a href="https://geeksofknowhere.com/en/tcp-checksum-header-data/" rel="prev"><span class="title"><i class=" fas fa-long-arrow-alt-left" aria-hidden="true" role="img"></i> Previous Post</span><span class="post-title">Tips For Resolving TCP Checksum Header Data</span></a></div></div>
</nav>
<section id="related-posts" class="clr">
<h3 class="theme-heading related-posts-title">
<span class="text">You Might Also Like</span>
</h3>
<div class="oceanwp-row clr">
<article class="related-post clr col span_1_of_3 col-1 post-157558 post type-post status-publish format-standard has-post-thumbnail hentry category-en entry has-media">
<figure class="related-post-media clr">
<a href="https://geeksofknowhere.com/en/gpx-mp3-player-error/" class="related-thumb">
<img width="211" height="300" src="https://geeksofknowhere.com/wp-content/uploads/2022/04/gpx-mp3-player-error-211x300.jpg" class="attachment-medium size-medium wp-post-image" alt="Read more about the article Steps To Get Rid Of GPX MP3 Player Error Problem" loading="lazy" itemprop="image" srcset="https://geeksofknowhere.com/wp-content/uploads/2022/04/gpx-mp3-player-error-211x300.jpg 211w, https://geeksofknowhere.com/wp-content/uploads/2022/04/gpx-mp3-player-error.jpg 451w" sizes="(max-width: 211px) 100vw, 211px" /> </a>
</figure>
<h3 class="related-post-title">
<a href="https://geeksofknowhere.com/en/gpx-mp3-player-error/" rel="bookmark">Steps To Get Rid Of GPX MP3 Player Error Problem</a>
</h3><!-- .related-post-title -->
<time class="published" datetime="2022-04-25T01:01:24+00:00"><i class=" icon-clock" aria-hidden="true" role="img"></i>April 25, 2022</time>
</article><!-- .related-post -->
<article class="related-post clr col span_1_of_3 col-2 post-153260 post type-post status-publish format-standard has-post-thumbnail hentry category-en entry has-media">
<figure class="related-post-media clr">
<a href="https://geeksofknowhere.com/en/how-to-catch-spyware/" class="related-thumb">
<img width="300" height="157" src="https://geeksofknowhere.com/wp-content/uploads/2022/04/how-to-catch-spyware-300x157.jpg" class="attachment-medium size-medium wp-post-image" alt="Read more about the article FIX: How To Catch Spyware" loading="lazy" itemprop="image" srcset="https://geeksofknowhere.com/wp-content/uploads/2022/04/how-to-catch-spyware-300x157.jpg 300w, https://geeksofknowhere.com/wp-content/uploads/2022/04/how-to-catch-spyware-1024x535.jpg 1024w, https://geeksofknowhere.com/wp-content/uploads/2022/04/how-to-catch-spyware-768x401.jpg 768w, https://geeksofknowhere.com/wp-content/uploads/2022/04/how-to-catch-spyware.jpg 1200w" sizes="(max-width: 300px) 100vw, 300px" /> </a>
</figure>
<h3 class="related-post-title">
<a href="https://geeksofknowhere.com/en/how-to-catch-spyware/" rel="bookmark">FIX: How To Catch Spyware</a>
</h3><!-- .related-post-title -->
<time class="published" datetime="2022-04-15T19:47:47+00:00"><i class=" icon-clock" aria-hidden="true" role="img"></i>April 15, 2022</time>
</article><!-- .related-post -->
<article class="related-post clr col span_1_of_3 col-3 post-13473 post type-post status-publish format-standard has-post-thumbnail hentry category-en tag-cmd-exe tag-exe tag-powershell tag-powershell-script tag-program tag-running tag-stop tag-task tag-taskkill tag-taskkill-command tag-taskkill-f tag-taskkill-pid tag-tasklist tag-wikihow tag-windows-powershell tag-windows-server entry has-media">
<figure class="related-post-media clr">
<a href="https://geeksofknowhere.com/en/command-to-kill-process-in-windows-7/" class="related-thumb">
<img width="300" height="152" src="https://geeksofknowhere.com/wp-content/uploads/2021/09/command-to-kill-process-in-windows-7-300x152.jpg" class="attachment-medium size-medium wp-post-image" alt="Read more about the article Steps To Fix The Command To Complete The Process In Windows 7" loading="lazy" itemprop="image" srcset="https://geeksofknowhere.com/wp-content/uploads/2021/09/command-to-kill-process-in-windows-7-300x152.jpg 300w, https://geeksofknowhere.com/wp-content/uploads/2021/09/command-to-kill-process-in-windows-7.jpg 640w" sizes="(max-width: 300px) 100vw, 300px" /> </a>
</figure>
<h3 class="related-post-title">
<a href="https://geeksofknowhere.com/en/command-to-kill-process-in-windows-7/" rel="bookmark">Steps To Fix The Command To Complete The Process In Windows 7</a>
</h3><!-- .related-post-title -->
<time class="published" datetime="2021-09-21T08:39:08+00:00"><i class=" icon-clock" aria-hidden="true" role="img"></i>September 21, 2021</time>
</article><!-- .related-post -->
</div><!-- .oceanwp-row -->
</section><!-- .related-posts -->
</article>
</div><!-- #content -->
</div><!-- #primary -->
<aside id="right-sidebar" class="sidebar-container widget-area sidebar-primary" itemscope="itemscope" itemtype="https://schema.org/WPSideBar" role="complementary" aria-label="Primary Sidebar">
<div id="right-sidebar-inner" class="clr">
<div id="search-2" class="sidebar-box widget_search clr">
<form role="search" method="get" class="searchform" action="https://geeksofknowhere.com/">
<label for="ocean-search-form-2">
<span class="screen-reader-text">Search this website</span>
<input type="search" id="ocean-search-form-2" class="field" autocomplete="off" placeholder="Search" name="s">
</label>
</form>
</div>
</div><!-- #sidebar-inner -->
</aside><!-- #right-sidebar -->
</div><!-- #content-wrap -->
</main><!-- #main -->
<footer id="footer" class="site-footer" itemscope="itemscope" itemtype="https://schema.org/WPFooter" role="contentinfo">
<div id="footer-inner" class="clr">
<div id="footer-widgets" class="oceanwp-row clr">
<div class="footer-widgets-inner container">
<div class="footer-box span_1_of_4 col col-1">
</div><!-- .footer-one-box -->
<div class="footer-box span_1_of_4 col col-2">
</div><!-- .footer-one-box -->
<div class="footer-box span_1_of_4 col col-3 ">
</div><!-- .footer-one-box -->
<div class="footer-box span_1_of_4 col col-4">
</div><!-- .footer-box -->
</div><!-- .container -->
</div><!-- #footer-widgets -->
<div id="footer-bottom" class="clr no-footer-nav">
<div id="footer-bottom-inner" class="container clr">
<div id="copyright" class="clr" role="contentinfo">
Copyright - OceanWP Theme by OceanWP </div><!-- #copyright -->
</div><!-- #footer-bottom-inner -->
</div><!-- #footer-bottom -->
</div><!-- #footer-inner -->
</footer><!-- #footer -->
</div><!-- #wrap -->
</div><!-- #outer-wrap -->
<a aria-label="Scroll to the top of the page" href="#" id="scroll-top" class="scroll-top-right"><i class=" fa fa-angle-up" aria-hidden="true" role="img"></i></a>
<!-- Start of StatCounter Code -->
<script>
<!--
var sc_project=12605795;
var sc_security="4e141349";
var sc_invisible=1;
var scJsHost = (("https:" == document.location.protocol) ?
"https://secure." : "http://www.");
//-->
</script>
<script type="text/javascript"
src="https://secure.statcounter.com/counter/counter.js"
async></script> <noscript><div class="statcounter"><a title="web analytics" href="https://statcounter.com/"><img class="statcounter" src="https://c.statcounter.com/12605795/0/4e141349/1/" alt="web analytics" /></a></div></noscript>
<!-- End of StatCounter Code -->
<script src='https://geeksofknowhere.com/wp-content/plugins/contact-form-7/includes/swv/js/index.js?ver=5.6.3' id='swv-js'></script>
<script id='contact-form-7-js-extra'>
var wpcf7 = {"api":{"root":"https:\/\/geeksofknowhere.com\/wp-json\/","namespace":"contact-form-7\/v1"}};
</script>
<script src='https://geeksofknowhere.com/wp-content/plugins/contact-form-7/includes/js/index.js?ver=5.6.3' id='contact-form-7-js'></script>
<script src='https://geeksofknowhere.com/wp-includes/js/imagesloaded.min.js?ver=4.1.4' id='imagesloaded-js'></script>
<script id='oceanwp-main-js-extra'>
var oceanwpLocalize = {"nonce":"8753784d96","isRTL":"","menuSearchStyle":"drop_down","mobileMenuSearchStyle":"disabled","sidrSource":null,"sidrDisplace":"1","sidrSide":"left","sidrDropdownTarget":"link","verticalHeaderTarget":"link","customSelects":".woocommerce-ordering .orderby, #dropdown_product_cat, .widget_categories select, .widget_archive select, .single-product .variations_form .variations select"};
</script>
<script src='https://geeksofknowhere.com/wp-content/themes/oceanwp/assets/js/theme.min.js?ver=3.3.5' id='oceanwp-main-js'></script>
<script src='https://geeksofknowhere.com/wp-content/themes/oceanwp/assets/js/drop-down-mobile-menu.min.js?ver=3.3.5' id='oceanwp-drop-down-mobile-menu-js'></script>
<script src='https://geeksofknowhere.com/wp-content/themes/oceanwp/assets/js/drop-down-search.min.js?ver=3.3.5' id='oceanwp-drop-down-search-js'></script>
<script src='https://geeksofknowhere.com/wp-content/themes/oceanwp/assets/js/vendors/magnific-popup.min.js?ver=3.3.5' id='ow-magnific-popup-js'></script>
<script src='https://geeksofknowhere.com/wp-content/themes/oceanwp/assets/js/ow-lightbox.min.js?ver=3.3.5' id='oceanwp-lightbox-js'></script>
<script src='https://geeksofknowhere.com/wp-content/themes/oceanwp/assets/js/vendors/flickity.pkgd.min.js?ver=3.3.5' id='ow-flickity-js'></script>
<script src='https://geeksofknowhere.com/wp-content/themes/oceanwp/assets/js/ow-slider.min.js?ver=3.3.5' id='oceanwp-slider-js'></script>
<script src='https://geeksofknowhere.com/wp-content/themes/oceanwp/assets/js/scroll-effect.min.js?ver=3.3.5' id='oceanwp-scroll-effect-js'></script>
<script src='https://geeksofknowhere.com/wp-content/themes/oceanwp/assets/js/scroll-top.min.js?ver=3.3.5' id='oceanwp-scroll-top-js'></script>
<script src='https://geeksofknowhere.com/wp-content/themes/oceanwp/assets/js/select.min.js?ver=3.3.5' id='oceanwp-select-js'></script>
<script src='https://geeksofknowhere.com/wp-content/plugins/easy-table-of-contents/vendor/smooth-scroll/jquery.smooth-scroll.min.js?ver=2.2.0' id='ez-toc-jquery-smooth-scroll-js'></script>
<script src='https://geeksofknowhere.com/wp-content/plugins/easy-table-of-contents/vendor/js-cookie/js.cookie.min.js?ver=2.2.1' id='ez-toc-js-cookie-js'></script>
<script src='https://geeksofknowhere.com/wp-content/plugins/easy-table-of-contents/vendor/sticky-kit/jquery.sticky-kit.min.js?ver=1.9.2' id='ez-toc-jquery-sticky-kit-js'></script>
<script id='ez-toc-js-js-extra'>
var ezTOC = {"smooth_scroll":"1","visibility_hide_by_default":"","width":"auto","scroll_offset":"30"};
</script>
<script src='https://geeksofknowhere.com/wp-content/plugins/easy-table-of-contents/assets/js/front.min.js?ver=2.0.34-1664989355' id='ez-toc-js-js'></script>
</body>
</html>