Table of Contents
Updated
If you have boing Boing malware error code on your computer, you should check out these troubleshooting ideas. The hugely popular Boing Boing blog, created by a stranger who injected malicious code into a WordPress website design template, was hacked on Friday. At about 11:30 am ET on January 10, an unknown person entered the Boing Boing CMS using the credentials of a Boing Boing team member.
Friday,
In the extremely popular boing blog, the boing website was hacked by an unknown 1 who injected malicious rules into the WordPress theme of the website.
At about 11:30 am ET on January 10th, an unknown person with the credentials of a member of the Boing boing.Ont team appeared at De cms Boing Boing an.Ont
They installed our theme widget, which immediately redirected them to a malicious site hosted by a third party.Users
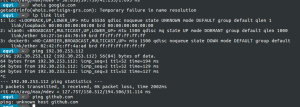
Users visiting the website from desktop computers reported that they were redirected directly to a download page for a malicious Adobe Flash update.

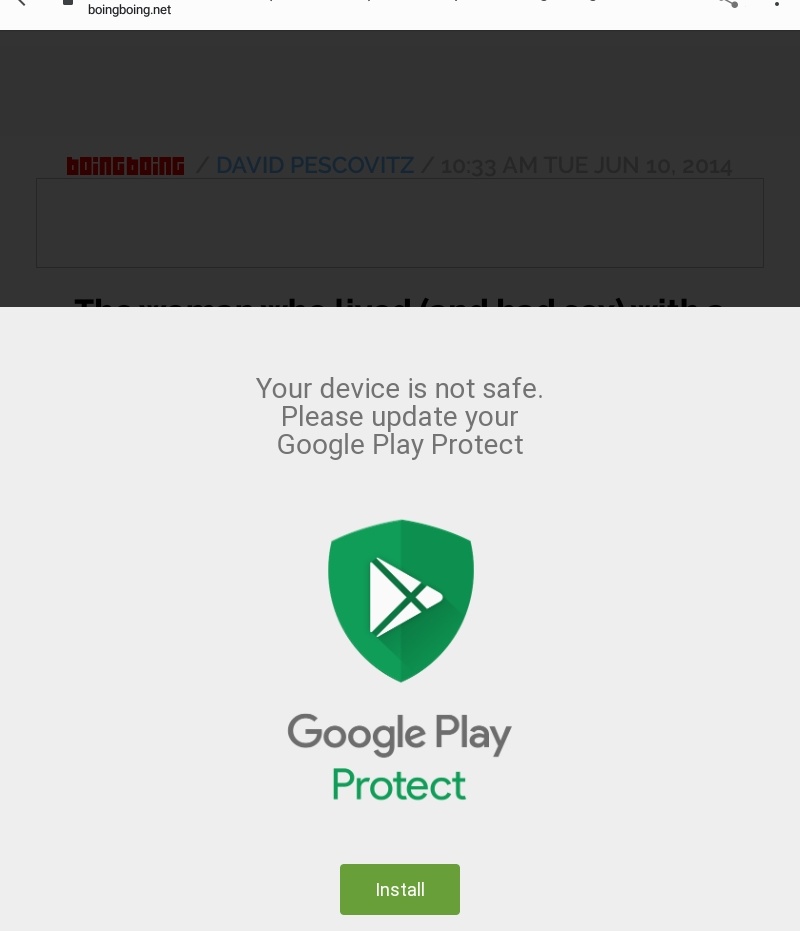
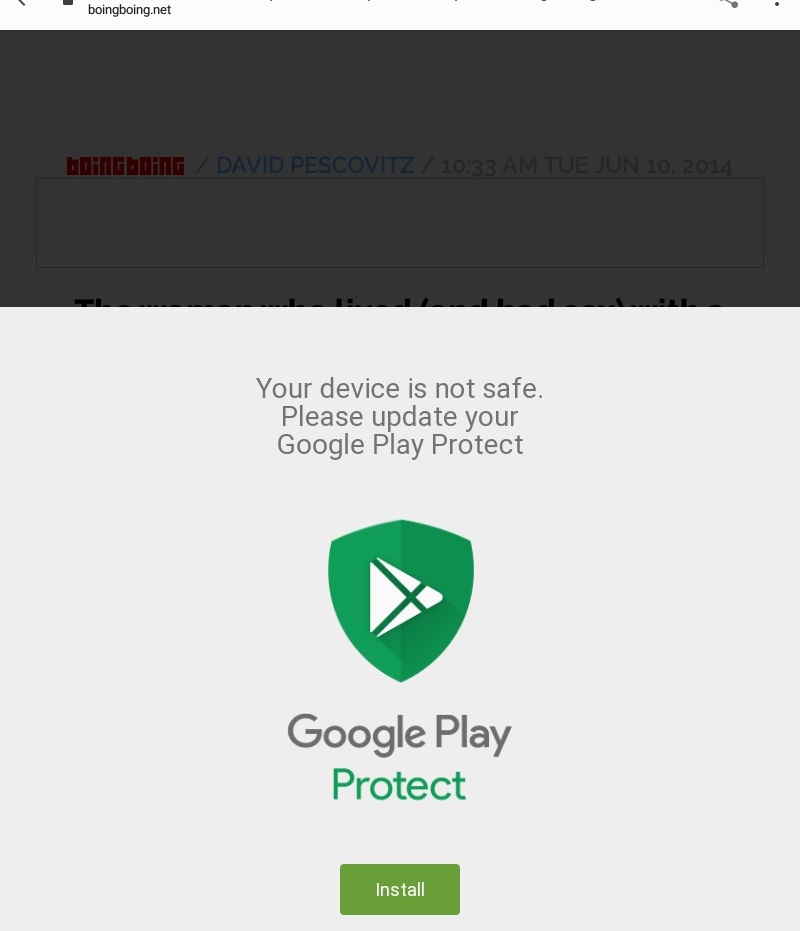
At the same time, Android users were getting a pop-up saying they were from Go to google, and that their phone was not secure.
These are not new ideas. Cybercriminals on the Internet have long tricked users into directly installing the code, passing it off as a genuine Adobe Flash update, a brand new update, or alerting the system owner to take action to restore a backup device.
C There are many obvious related questions that sometimes need to be asked. Getting Started:
Boing Boing claims to have removed that virus and changed its users’ credentials. Oddly enough, they say they only keep employee activity account logs for 72 hours again, which seems risky to me:
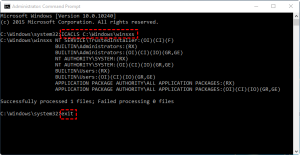
“The little BB class then proceeded to change passwords, access the wedding reception, validate access rights, and search the web for a behavior log. As stated in According to our privacy policy, we keep logs for 72 hours, but this was enough to monitor the overall activity of malicious user accounts and respond accordingly. We also went into the details of modifying our CMS to ensure that only one separate audit trail (besides our 72 – hourly access logs) are stored over time to help us track administrative steps in our version of the software for future violations. So we can take action and take further action in the future.”
Besides these creases, it’s nice to see how Boing demonstrates how Boing warns its users immediately by demonstrating this issue and using transparency.
If someone has visited the Boing Boing website in the past few days and is concerned that their computer has been compromised, they may want to run the latest antivirus software.
Graham – Cluley is a veteran of the antivirus community who has worked in security for a number of retailers since the early 1990s when he downloaded the very first version of Dr. Solomon’s Antivirus Toolkit for Windows. A freelance security analyst, he regularly speaks to the media and is a leading international speaker on cybercriminals on the Internet, online security and privacy.Follow him on Twitter at or @gcluley email him one by one at.
Over the weekend, BoingBoing viewers reported strange pop-ups advising visitors to install Google Play Protect. Some pop-ups told users that Protect-Google needed to be updated, and ads and marketing pop-ups urged users to comply with Adobe requirements. After clicking the “Install” button, end users should be redirected to a fake Adobe Wizard installation page, redirecting users toand the Adobe Flash Companion Player at this URL is h**ps://flashpliayers.* ***/software/download.php? key=Fp38.46.544775
Another user reported that the downloaded and installed .exe file shows the strange computer .txt file that we see in Pastebin. The same user said that it looks like the hackers used 7z SFX Constructor from this site Http://usbtor **ru/viewtopic.sent php?t=798 exe to request ***430lodsposlokstore< /p>
Today, BoingBoing reported that most of its websites were hacked every last weekend. In their statement, they urged malware visitors to run local antivirus software.
In their statement, they said: “An unknown party logged into Boing.de Boing.CMS using the credentials of a member of the Boing.Boing team. setting they allowed the market to redirect malicious users to a site hosted by a third party” .
BoingBoing also said about the malware that while it didn’t show ads, it looked like it was from the company that was showing the ads. “But in the end, it allowed our advertising partner to give us the details of the entire a kaki. BoingBoing did this without explaining how the advertising partner knew the details about the malware.
Speed up your computer today with this simple download.보잉 보잉 악의? 즉시 수정
Boeing-boing Boosaardigheid? Repareer Het Onmiddellijk
Boeing-boing Malveillance ? Corrigez-le Immédiatement
Malícia Boeing-boing? Corrija-o Imediatamente
Boeing-boing Złośliwość? Napraw To Natychmiast
Boeing-boing Bosheit? Repariere Es Sofort
¿Malicia De Boeing-boing? Arreglarlo De Inmediato
Malizia Da Boeing? Risolvilo Immediatamente
Боинг-боинг злоба? Исправьте это немедленно
Boeing-boing Illvilja? Fixa Det Omedelbart