Table of Contents
Updated
In this user guide, we will describe some of the possible causes that can cause the win32 vampire and then I will show how you can try to get rid of this problem. Summary. Microsoft Defender Antivirus detects such a threat. This generic indecisive behavior detection is designed to detect potentially malicious files. If you’ve downloaded a file or received it via email, make sure it’s from a trusted source before you open it.
Alias
- IM-Worm.Win32.Vampa.c
- W32/Vampa@MM
- W32.Vampa
Properties
- Sets the registry itself
Affected Operating Systems
Recovery Instructions:
On Windows, you must also edit the following registry image for each user that Anti-Malware is running. Removing this entry is recommended on Windows 95/98/Me. Read the note about changing the registry.
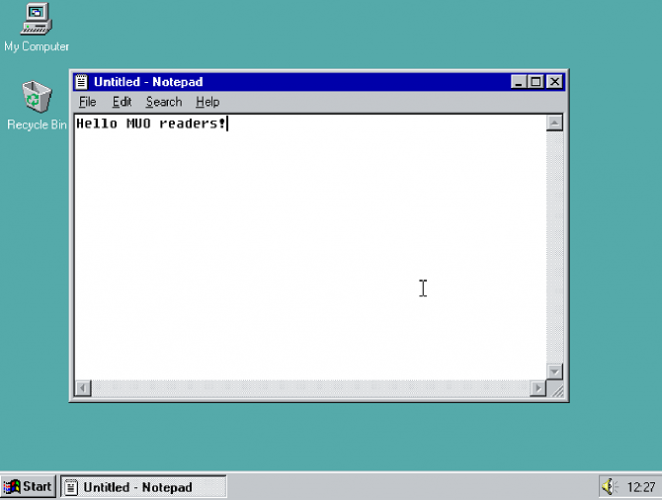
On the taskbar, click Start|Run. Type “regedit” and press Enter. The Registry Editor will open.
Before changing the PC registry, you need to create a backup copy. From the Registry menu, select Export Registry File. In the “Export” section, click “And that’s it”, just save to the registry as a backup.
Each user contains a registry area named HKEY_USERS[user ID]. Find the entire entry for each user:
(W32/Vampa@MM, I-Worm/Vampa, System Error, Win32/Vampa win32/vampire!worm,.A!Worm, WORM_VAMPA.B, IM-Worm.Win32.Vampa.b, W32.Vampa , IRC-Worm.Vampire, IM-Worm.Win32.Vampa.a, Ver/Vampa.A, Win32/ICQ.Vamp.A!Worm, Win32/ICQVampa.A, IM-Worm.Win32.Vampa.c, Ver /ICQVampire.Srv, Win32.HLLW.ICQ.Vampa.b, WORM_VAMPA.A, Win32.HLLW.Vampa.a)
Virus sketch added: Itemprop=”datePublished”>2006-02-01
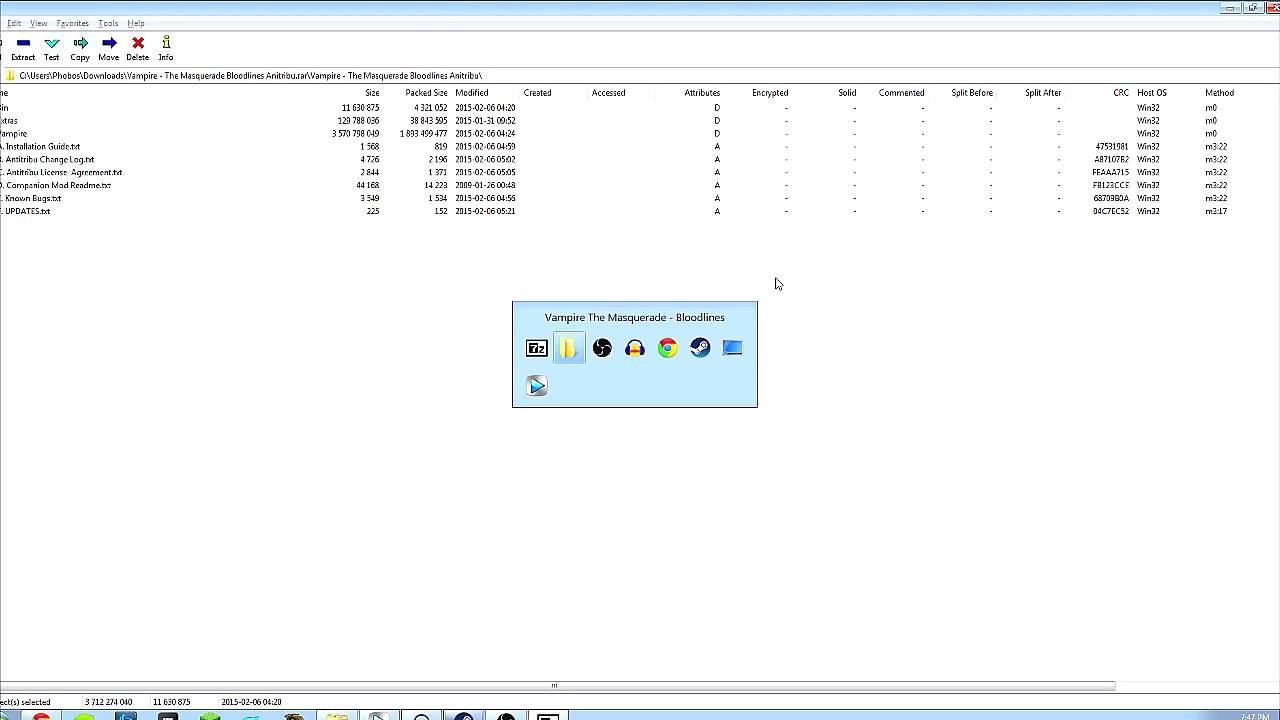
E:steamsteamappscommonvampire masquerade, which is no doubt bloodlinesvampire.exe is not a legal Win32 application.
Is there anyone who is doing this? he offers the same Readabilitydatatable=”1″>
Vampire Alias (alias):
What is Win32 Banker virus?
Win32/Banker passes the stolen information to the zeroer in several ways, including sending an important email to the attacker, uploading the stolen information to the hacker’s FTP site, and sending the information to the hacker via HTTP to your POST.
How Vampire Your Computer Is ^
In order to completely remove Vampire from your computer, you need toWe need to delete folders and files containing Vampire. These files and folders are listed in the Advanced File Folders sections of this page, respectively.
For instructions on deleting vampire files and folders, see “How to delete vampire files (.exe, .dll, etc.)” below.
How To Delete Vampire Files (.exe, .dll, Etc.) ^ Folders With
Vampire related 
are listed in the folders and sections of this page. Your every
- Browse the file in the folder specified by others in sections using Image Explorer.
Note: Paths use some special versions (conditions), such as [%program_files%]. Pay attention to these conventions depending on the version/language of Windows. These conventions are shown Win32 Vampiro
Win32 Vampier
Win32 Vampiro
Vampire Win32
Win32 Вампир
Win32 Wampir
Win32 뱀파이어
Win32 Vampyr
Win32-Vampir
Vampiro Win32